The Best WordPress SEO Plugin and Toolkit
Join 3,000,000+ Professionals who use AIOSEO to Improve Their Website Search Rankings.
Optimizer
(Schema)
Sitemaps
SEO
SEO
Modules
Finally, a WordPress SEO Plugin that’s Easy and Powerful
All in One SEO is the best WordPress SEO plugin. Here are the features that makes AIOSEO the most powerful and user-friendly WordPress SEO plugin in the market.
Get the #1 Most Powerful WordPress SEO Plugin Today
Join over 3 million smart website owners who use AIOSEO to improve their website search rankings.
All-in-One SEO is a great product. I have been using it on all my WP sites for several years. I highly recommend it.

Robust without nagging or bloat. All-in-One SEO has been my go-to SEO plugin for over a decade. It was the first one I used, though I later tried some others. But I’ve come back to All-in-One time and again.

10 years using it allows me to say it is the best SEO plugin out there, we even have it in a yearly automated renewal basis. Keep up the great work!

Top 7 Reasons Why Over 3 Million Users ❤ AIOSEO
AIOSEO is the perfect WordPress SEO plugin for YOU. Here’s why over 3,000,000+ smart business owners, marketers, and web developers love All in One SEO plugin for WordPress, and you will too!
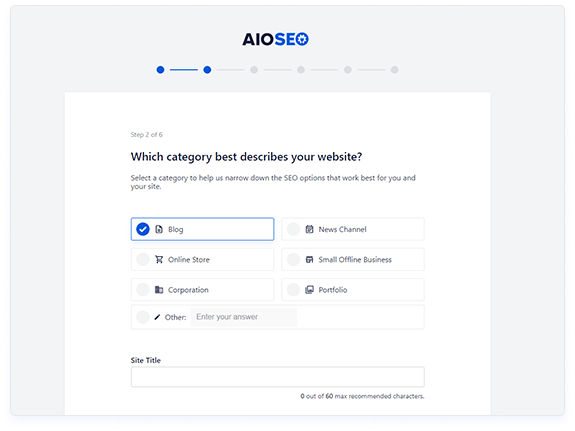
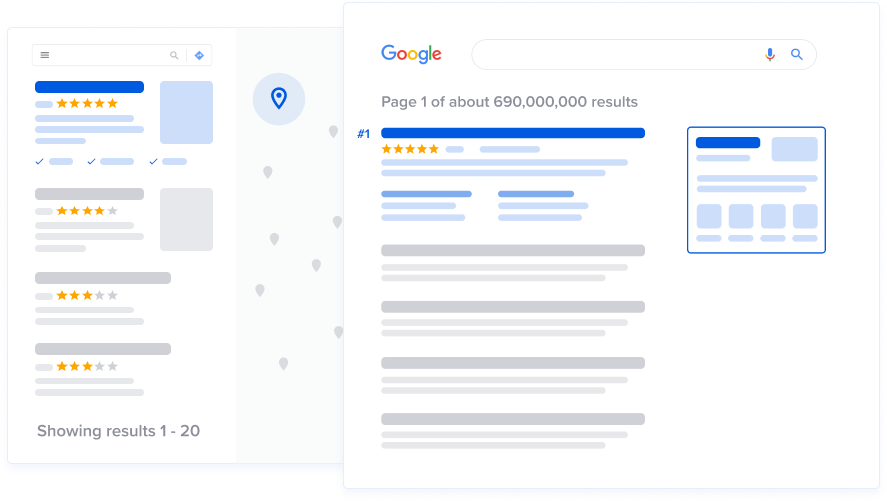
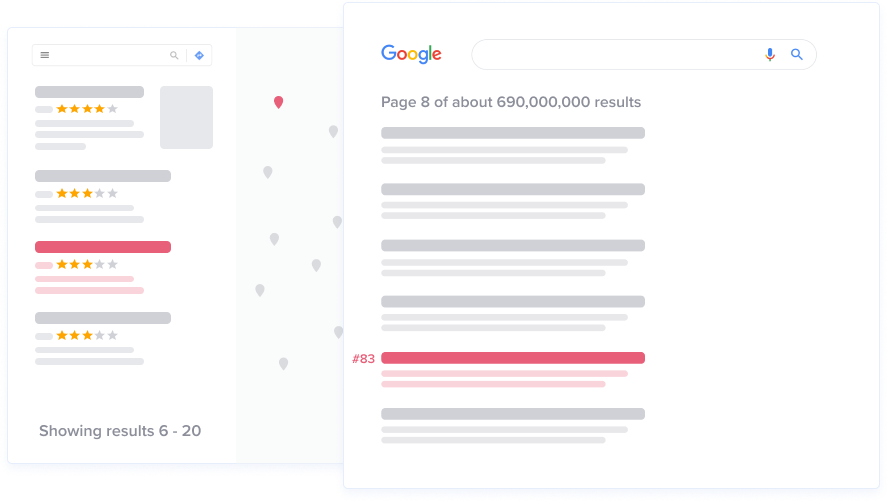
Properly Set Up WordPress SEO Without Hiring an Expert
AIOSEO makes it easy to set up the proper SEO foundations in less than 10 minutes. Our smart setup wizard optimizes your website’s SEO settings based on your unique profile.
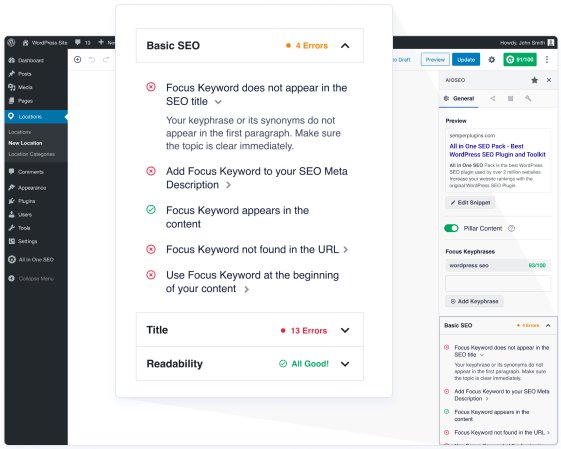
Easily Optimize Your Pages for Higher Rankings with TruSEO Score
TruSEO Score gives you a more in-depth analysis into your optimization efforts than just a pass or fail. Our actionable checklist helps you to unlock maximum traffic with each page.
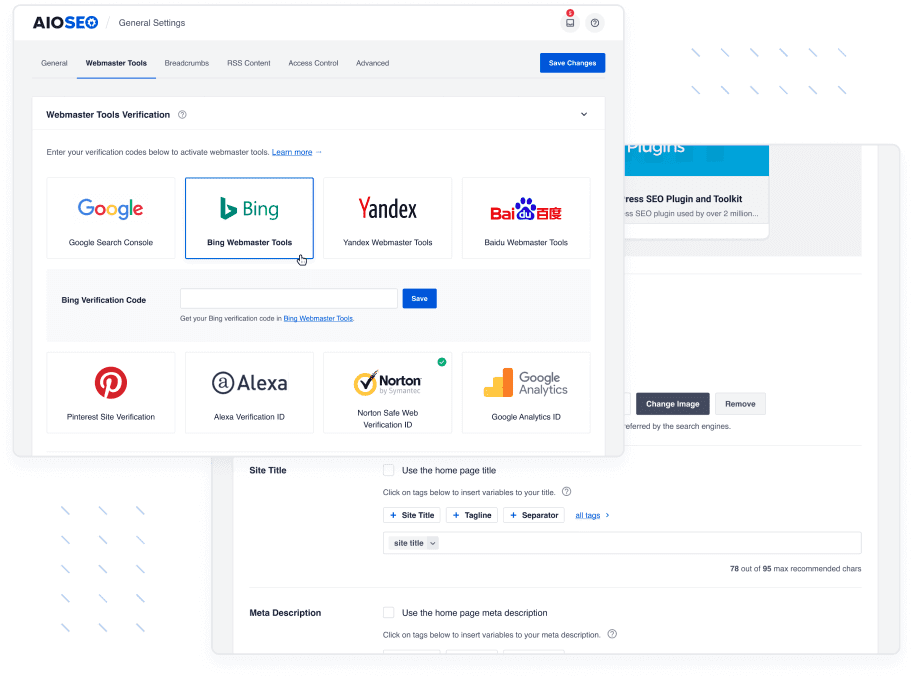
Seamless Integrations With All Your Favorite Tools
All in One SEO offers seamless integration with popular social media platforms like Facebook, Twitter, Pinterest, and more.
We also make it easy to connect with Google Search Console, Google AMP, and integrate with many popular WordPress plugins including WooCommerce, MemberPress, and more.
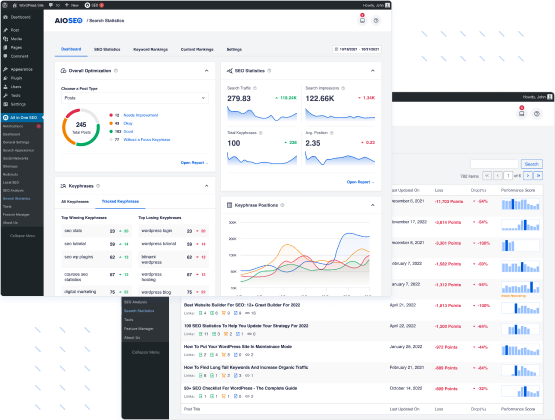
Track SEO Rankings and See Helpful SEO Metrics in One Place
All in One SEO gives you valuable data and actionable insights effortlessly with our advanced Search Statistics feature right inside your WordPress dashboard.
Monitor your website’s performance, keep track of keyword rankings, analyze search trends, and receive comprehensive reports on content decay.
Stay one step ahead of the competition and optimize your website’s SEO strategy for maximum results.
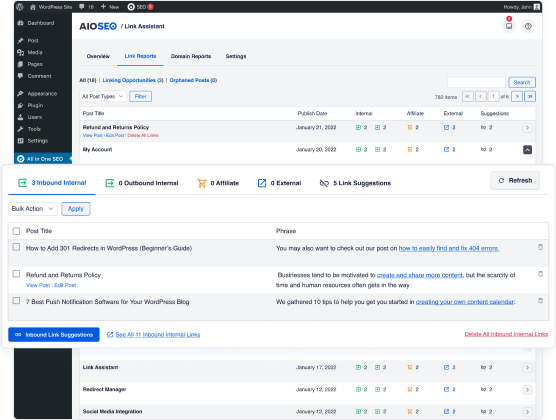
Save Time with Automated Link Assistant to Build More Links
Using intelligent automation, the All in One SEO Link Assistant scans your content, identifies relevant link opportunities, and seamlessly adds internal links saving you time.
The powerful features of our Link Assistant are integrated directly within WordPress, making link building a breeze.
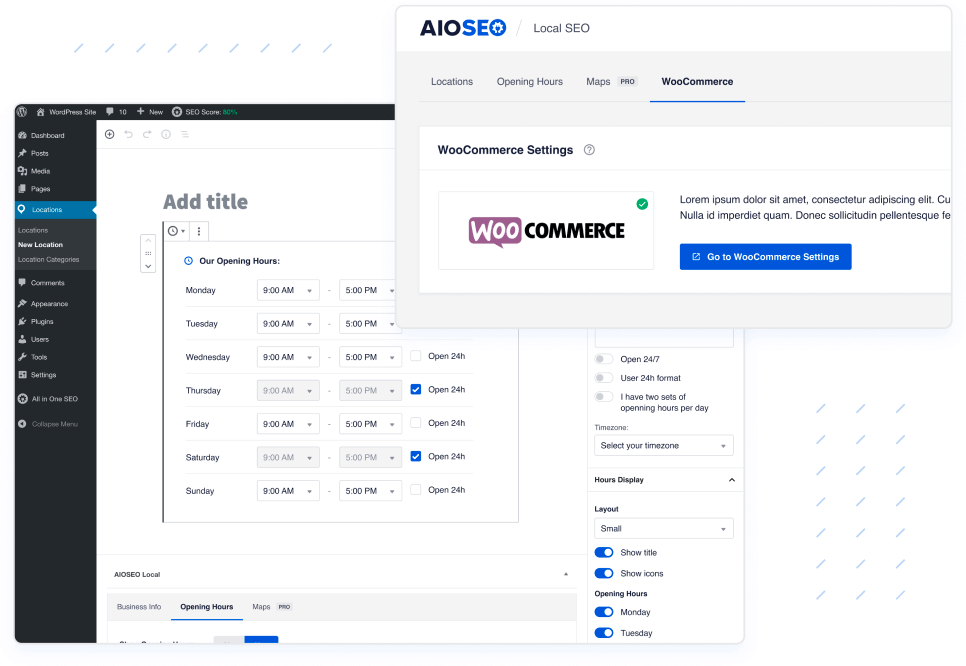
Support for Local SEO and WooCommerce SEO
All in One SEO offers complete support for Google Knowledge Graph and Schema.org markup for local businesses.
You can also easily optimize your WooCommerce product pages, product categories, and more.
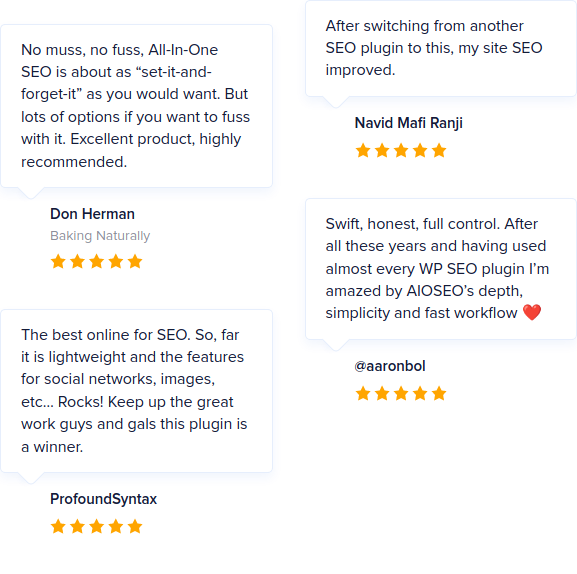
Top Rated Plugin + Exceptional Customer Support
Over 3 million websites use our WordPress SEO plugin to grow their traffic and revenue.
With over 3,000 5-star reviews, our support team has been recognized for industry-leading ratings from our customers.
Improve your WordPress SEO Rankings with AIOSEO
Get the most powerful All in One WordPress SEO plugin and improve your website search rankings today.
Frequently Asked Questions and Resources
Do you have a question about AIOSEO? See the list below for our most frequently asked questions. If your question is not listed here, then please contact us.
All in One SEO is a perfect WordPress SEO plugin for business owners, bloggers, designers, developers, photographers, and basically everyone else. If you want to optimize your WordPress SEO, then you need to use All in One SEO Pack for WordPress.
All in One SEO is a WordPress SEO Plugin. In order to use All in One SEO pack, you must have a self-hosted WordPress site. That’s all.
Absolutely not. You can optimize your WordPress SEO without any coding knowledge. All in One SEO is one of the most beginner friendly WordPress SEO plugin.
Absolutely not. All in One SEO WordPress plugin is carefully built with performance in mind. We have developed everything with performance best practices and modern standards to ensure things run smooth and fast.
Yes, All in One SEO has full translation and localization support. Our WordPress SEO plugin is translated into 10 languages with many more on the way.
No. All in One SEO is a WordPress SEO plugin, so it will NOT work on sites that do not use WordPress.
Yes, All in One SEO works with WordPress.com. Please be aware that only Business Plan users are able to install custom plugins on WordPress.com.
You can find installation instructions for WordPress.com sites here.
Yes, you can use All in One SEO WordPress plugin on client sites in two ways. Either you can purchase the Pro / Agency license OR purchase an appropriate license for each client sites. You can also refer your clients to purchase our WordPress SEO plugin directly from our site using your affiliate link to earn a 20% commission.
Yes, we do offer a free version of our powerful WordPress SEO plugin. You can download AIOSEO free WordPress SEO plugin directly from the WordPress.org site.
Need Help Improving Your WordPress SEO?
Take a look at AIOSEO Blog for tips & tricks on how to improve your WordPress SEO Rankings.


